Arch Linux - Docker Node - Network Breakdown - ( Part III )

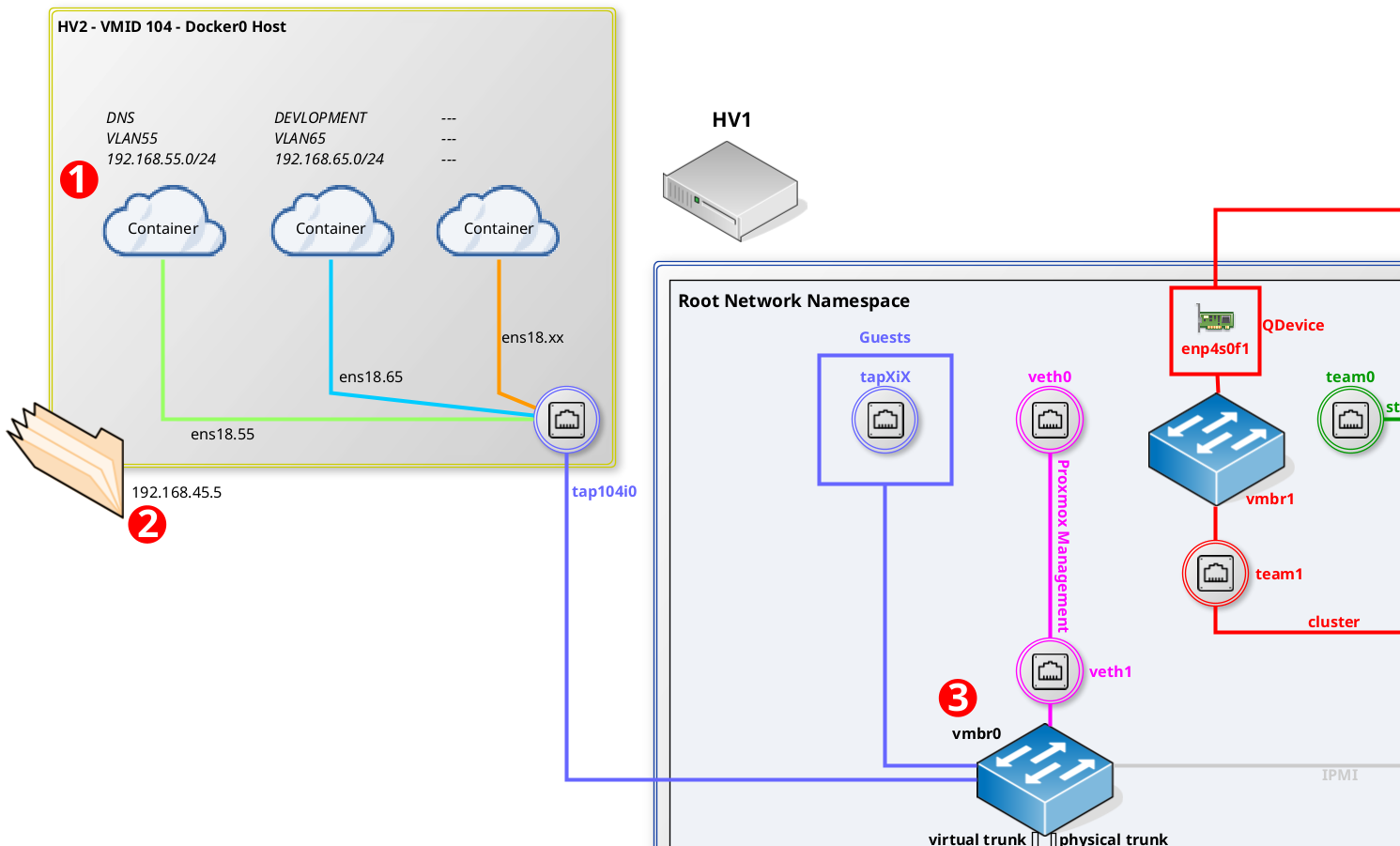
Let's examine the docker VM from the container to the proxmox host perspective.
1) Pihole Container - 192.168.55.10
[root@docker0 ~]# docker exec -ti pihole bash
root@pihole:/# ip -c l
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN mode DEFAULT group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
11: eth0@if4: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP mode DEFAULT group default
link/ether 02:42:c0:a8:37:0a brd ff:ff:ff:ff:ff:ff link-netnsid 0
root@pihole:/# ip -c addr
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
11: eth0@if4: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 02:42:c0:a8:37:0a brd ff:ff:ff:ff:ff:ff link-netnsid 0
inet 192.168.55.10/24 brd 192.168.55.255 scope global eth0
valid_lft forever preferred_lft forever2) Docker0 - 192.168.45.5
[root@docker0 ~]# ip -c l
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN mode DEFAULT group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
2: ens18: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP mode DEFAULT group default qlen 1000
link/ether 5a:a4:8c:e9:00:83 brd ff:ff:ff:ff:ff:ff
altname enp0s18
3: docker0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN mode DEFAULT group default
link/ether 02:42:32:86:1d:e8 brd ff:ff:ff:ff:ff:ff
4: ens18.55@ens18: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP mode DEFAULT group default
link/ether 5a:a4:8c:e9:00:83 brd ff:ff:ff:ff:ff:ff
[root@docker0 ~]# ip -c addr
1: lo: <LOOPBACK,UP,LOWER_UP> mtu 65536 qdisc noqueue state UNKNOWN group default qlen 1000
link/loopback 00:00:00:00:00:00 brd 00:00:00:00:00:00
inet 127.0.0.1/8 scope host lo
valid_lft forever preferred_lft forever
inet6 ::1/128 scope host
valid_lft forever preferred_lft forever
2: ens18: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc fq_codel state UP group default qlen 1000
link/ether 5a:a4:8c:e9:00:83 brd ff:ff:ff:ff:ff:ff
altname enp0s18
inet 192.168.45.5/24 brd 192.168.45.255 scope global ens18
valid_lft forever preferred_lft forever
inet6 fe80::58a4:8cff:fee9:83/64 scope link
valid_lft forever preferred_lft forever
3: docker0: <NO-CARRIER,BROADCAST,MULTICAST,UP> mtu 1500 qdisc noqueue state DOWN group default
link/ether 02:42:32:86:1d:e8 brd ff:ff:ff:ff:ff:ff
inet 172.17.0.1/16 brd 172.17.255.255 scope global docker0
valid_lft forever preferred_lft forever
inet6 fe80::42:32ff:fe86:1de8/64 scope link
valid_lft forever preferred_lft forever
4: ens18.55@ens18: <BROADCAST,MULTICAST,UP,LOWER_UP> mtu 1500 qdisc noqueue state UP group default
link/ether 5a:a4:8c:e9:00:83 brd ff:ff:ff:ff:ff:ff
inet6 fe80::58a4:8cff:fee9:83/64 scope link
valid_lft forever preferred_lft forever3) HV2 - Bridge VLAN - 192.168.1.101
hv2-ssh@hv2:~$ bridge v s
port vlan ids
enp4s0f0 15 PVID Egress Untagged
vmbr0 None
veth1 2 PVID Egress Untagged
team2 2
15
25
35
45
55
201
tap101i0 2
15
25
35
45
55
201
tap100i0 45 PVID Egress Untagged
tap103i1 45 PVID Egress Untagged
tap105i0 45 PVID Egress Untagged
tap106i0 45 PVID Egress Untagged
tap104i0 45 PVID Egress Untagged
554) Firewall
Follow the article below to create a new VLAN on the firewall.
https://blog.infoitech.co.uk/proxmox-tucana-cloud/
Resources
libnetwork/macvlan.md at master · moby/libnetwork
networking for containers. Contribute to moby/libnetwork development by creating an account on GitHub.
![Infoitech - [B]logging](https://blog.infoitech.co.uk/content/images/2021/04/youtube-small-cover-1.png)

